Configure two-factor authentication on a Windows server with the RD Gateway service
This article describes how to configure a Windows server to enable two-factor authentication when Remote Desktop Authentication (RDP) is connected to the RD Gateway service.
RD Gateway — a Windows server component that allows you to connect to the desktop through a gateway that performs VPN functions, which is to create an encrypted connection over the TLS protocol. In addition, the gateway allows you to limit session timeout, control user access to drives, USB, clipboard, printer and network resources.
Applicable for versions:
Windows Server 2012 R2Windows Server 2016Windows Server 2019
Possible authentication methods:
TelegramThe call (to accept the call and press #)Mobile application (soon)
To configure the second authentication factor, you need to install and configure MultiFactor Radius Adapter.
Operation Principle
- The user connects to the remote desktop via the RD Gateway;
- The RD Gateway uses Network Policy Server (NPS) access settings;
- the NPS receives a request from the RD Gateway, forwards the MultiFactor Radius Adapter component;
- The component makes a callback to the NPS to check the user login and password.
- NPS receives a request from a component, checks the user login and password, and access policies
- The component sends a login confirmation request to the user's phone;
- The user confirms the request in the phone and connects to the VPN.
Installing services
You will need Windows Server with Remote Desktop Gateway and Network Policy and Access Service components installed. The server can run autonomously or in a domain.
The installation process is detailed in multiple sources, use for example this comprehensive article.
Installation of the server certificate
To encrypt the traffic between the client and the server, as well as to authenticate the server, a certificate issued by a public certification authority is required. You can buy such certificate or get it for free in Let's Encrypt. How to do this in 5 minutes — read our article.
Setting up Remote Desktop Gateway
In Server Manager, open Tools -> Remote Desktop Services -> Remote Desktop Gateway Manager.
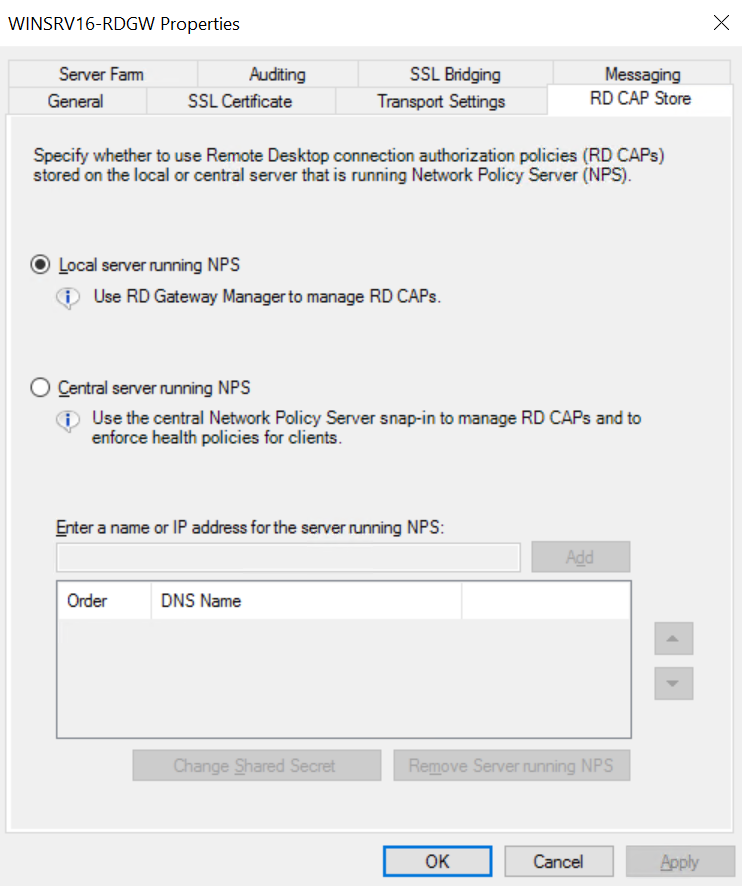
Next, under Policies -> Connection Authorization Policies, click on the right side of Configure Central RD CAP.
On the RD CAP Store tab, click the Local Server Running NPS option.
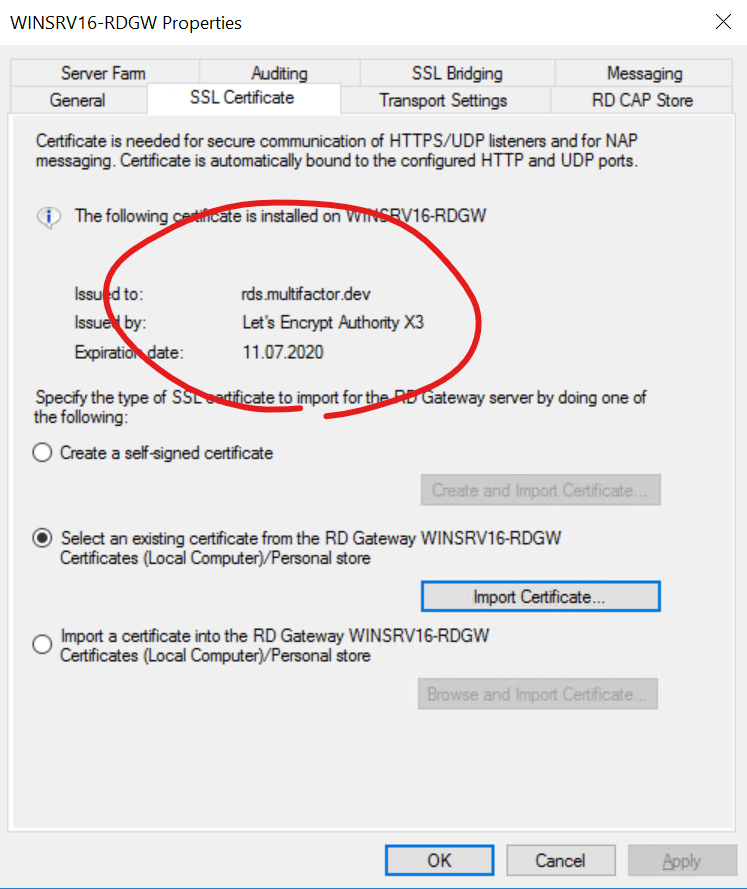
On the "SSL Certificate" tab, make sure that a valid certificate is installed.
Save and close
NPS Setting
RADIUS Proxy
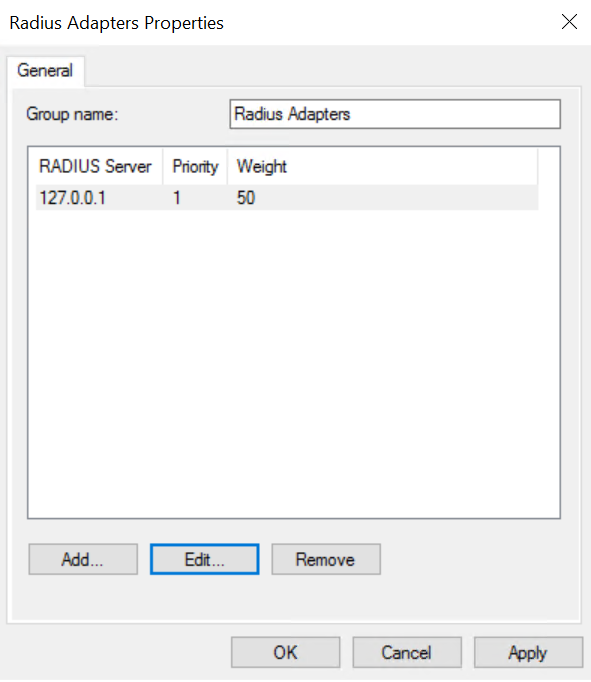
It is necessary to create a setting for proxying a request from RD Gateway to MultiFactor Radius Adapter.
Open the Server Manager -> Tools -> Network Policy Server.
- From the RADIUS Clients and Servers menu, select Remote RADIUS Server Groups.
- Create a new group
- Title: Radius Adapters
- Add a new Radius Server
- Address: Address of the component MultiFactor Radius Adapter
- Shared secret: from component settings
- Load Balancing: 40-second timeouts
- Save and close.
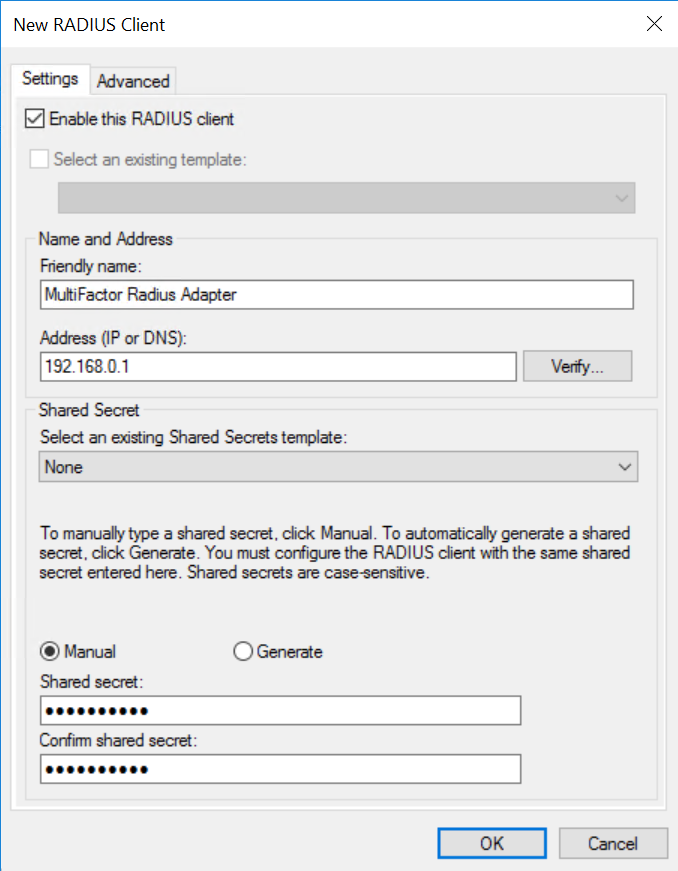
Radius Client
Describe the MultiFactor Radius Adapter as a RADIUS client so that NPS will accept requests from it.
- In me RADIUS Clients and Servers select RADIUS Clients.
- Create a new client:
- Friendly name: MultiFactor Radius Adapter
- Address: from component settings
- Shared Secret: from component settings
- Save and close.
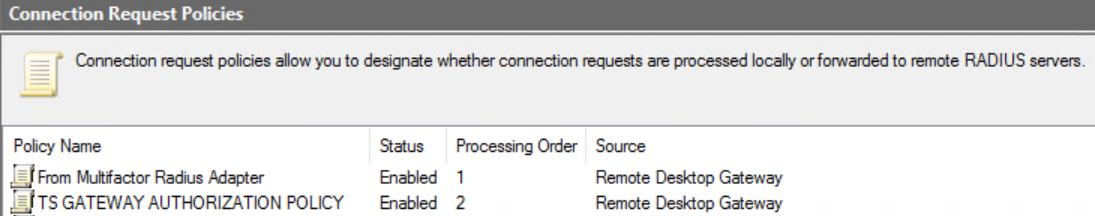
Connection request policies
We need two policies: one to accept requests from the RD Gateway and proxy to the MultiFactor Radius Adapter component, the other to accept requests from the component and authentication in the domain.
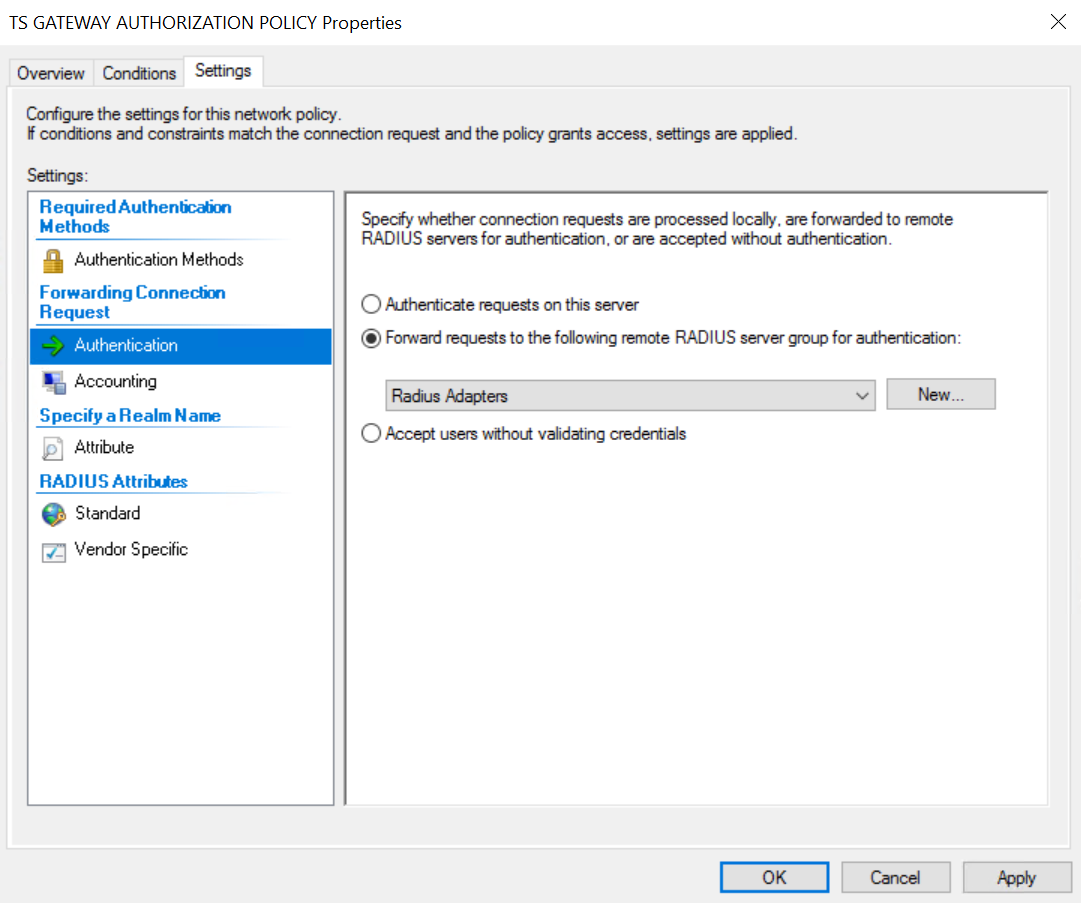
- In the Connection Request Policies section, open the properties of "TS GATEWAY AUTHORIZATION POLICY" &mdash policy; this policy is created automatically and is responsible for processing connection requests from RD Gateway.
- On the Settings -> Authentication tab, select "Forward requests to the following remote RADIUS server group for authentication";
- Save and close.
- Create a new policy for processing requests from a component:
- Policy name: From Multifactor Radius Adapter;
- Type of network access server: Remote Desktop Gateway;
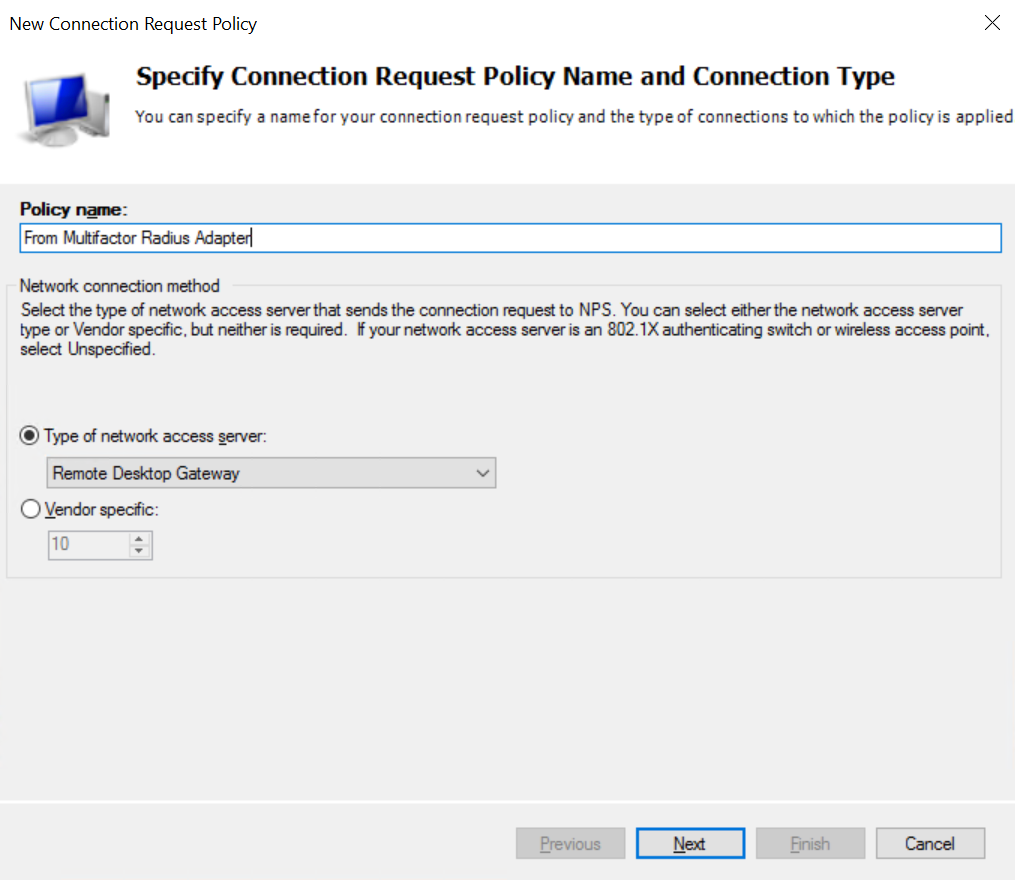
- In the next step, add a condition:
- Client Friendly Name — MultiFactor Radius Adapter;
- The rest of the default steps;
- Save and close.
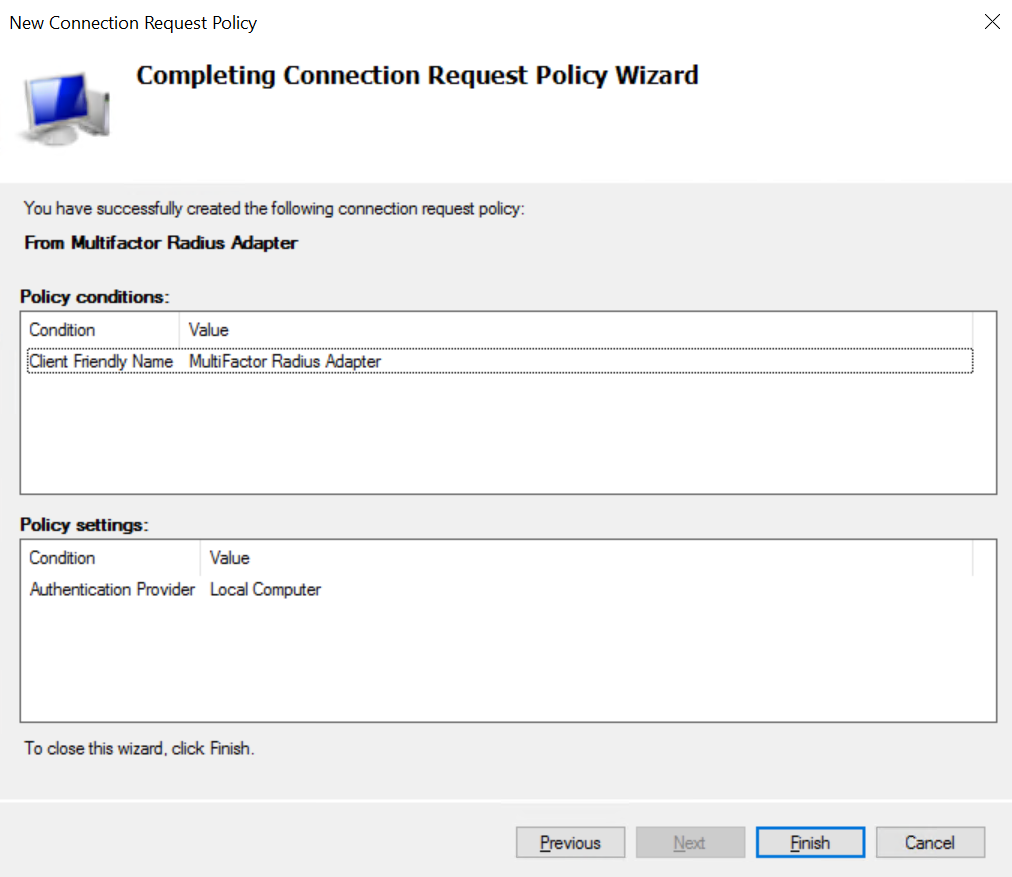
- Move the "From Multifactor Radius Adapter" policy to a level higher than "TS GATEWAY AUTHORIZATION POLICY".
Setting up Multifactor Radius Adapter
Specify the first factor of &mdash authentication; Radius and configure the NPS connection
Client Configuration
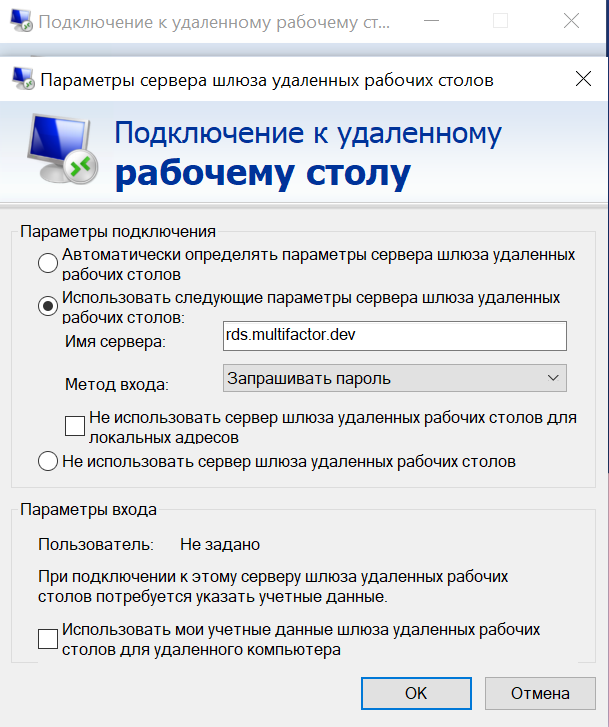
Open the connection to the remote desktop (mstsc.exe);
- Specify the address of the computer you want to connect to;
- click "Options" on the "Advanced" tab;
- Enter the gateway address
- Start the connection, enter the login and password with the domain
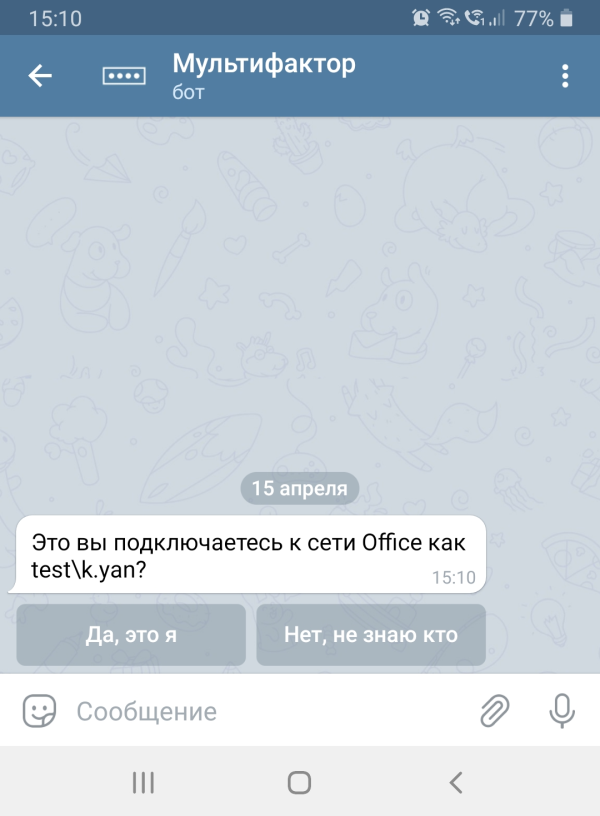
- A request will be received from the Multifactor to confirm access.
If something's not working
- Check the Windows log, Custom Views -> Server Roles -> Network Policy And Access Services.
- Check the log of the component MultiFactor Radius Adapter.
- Check the log Multifactor
Look at this: